What is Endpoint Encryption?
When it comes to encrypting data, there are various encryption strategies.
Disk encryption protects a hard drive in the event of theft or accidental loss by encrypting the entire disk including swap files, system files,
and hibernation files. If an encrypted disk is lost, stolen, or placed into another computer, the encrypted state of the drive remains
unchanged, ensuring only an authorized user can access its contents.
Some endpoint encryption solutions (like Symantec™ Endpoint Encryption) also include support to encrypt files stored on or copied to
removable media devices. As with disk encryption, removable media encryption helps prevent unauthorized access to information on lost or
stolen devices (in this case the devices are USB flash drives, external hard drives (USB, FireWire, and eSATA), SD cards, and compact flash
cards). In this way, organizations can benefit from the productivity gains associated from collaboration using removable storage without
putting data at risk.
How Disk Encryption Works
During the startup process of an operating system, a boot sequence is executed. The boot system is the initial set of operations that the
computer performs when it is switched on. A boot loader (or a bootstrap loader) is a short computer program that loads the main operating
system for the computer. The boot loader first looks at a boot record or partition table, which is the logical area “zero” (or starting point) of
the disk drive.
Disk encryption modifies the boot sector. For example, a computer protected with Symantec™ Endpoint Encryption presents a modified preboot
environment for the user to authenticate to the computer.
This modified pre-boot screen prompts the user for authentication credentials in the form of a passphrase (typically a longer password, often
resembling a sentence). At this point, the computer may ask for additional credentials such as a smart card, token, or other two-factor
authentication.
After the user enters valid authentication credentials, the operating system continues to load as normal and the user can access the
computer.
Most disk encryption software operates in conjunction with the file system architecture. It filters I/O operations for one or more file systems
or file system volumes.
When a drive is encrypted for the first time, it converts unencrypted drive blocks into encrypted blocks one at a time. Disk encryption allows
users to continue working as normal during this initial encryption process by varying the amount CPU power assigned to the initial encryption
process.
When a user accesses a file, disk encryption decrypts the data in memory before it is presented for viewing. If the user makes any changes to
the file, the data is encrypted in memory and written back to the relevant disk drive block just as it would be without encryption. Decrypted
data is never available on the disk. The encryption/decryption process happens at such a speed that it appears completely transparent to the
User.
How Removable Media Encryption Works
Removable media encryption software provides the ability to encrypt files on removable storage devices.
When a user copies files of a system onto a removable storage device, each file is encrypted to a password, a shared key or a certificate. At
the same time, utilities for Windows or Mac systems can be copied (if permitted by policy) allowing authorized access to data without the
endpoint client installed on a machine.
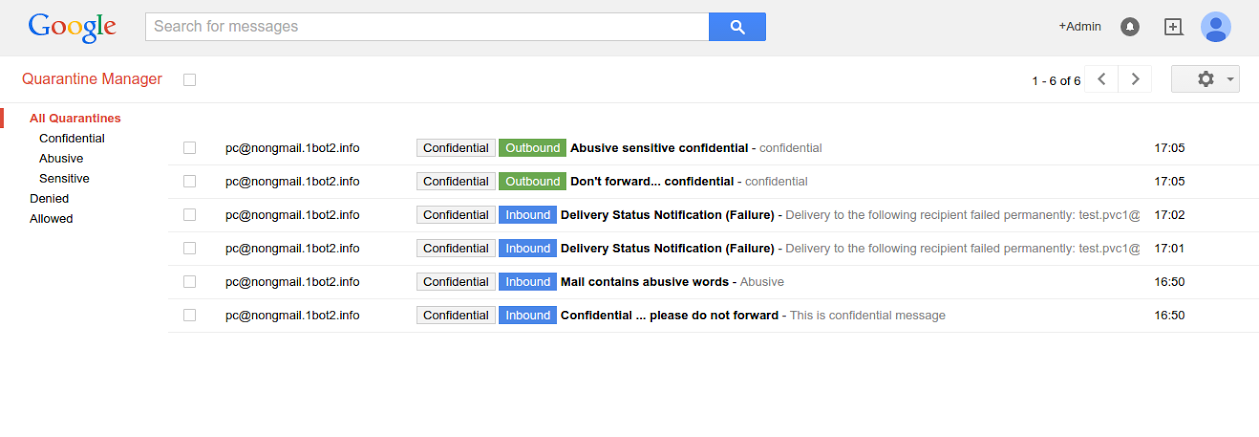
This file encryption can be governed by policy, user action, or Symantec DLP. In the case of Symantec DLP, the Endpoint Prevent software
monitors users’ machines and understands when a person is moving a sensitive file off his computer. With the integration of Symantec DLP
and Symantec Endpoint Encryption, administrators can ensure files with sensitive information that are moving to removable media are
encrypted rather than blocked, allowing business processes to continue in a secure manner.
To access the information, when the user inserts a removable media device like a USB drive with encrypted files into a computer system, the
removable media encryption software will prompt for passphrase, and upon successful authentication, the user can access the file.
Key Features
- Built PGP Strong – High performing, strong encryption, built with PGP Hybrid Cryptographic Optimizer (HCO) technology and leveraging AES-NI hardware optimization for even faster encryption speeds.
- Robust Reporting – Administrators can take advantage of out-of-the-box compliance reports or customize their own reports to help ease the burden of proof to auditors and key stakeholders.
- Active Directory Support – Individual and group policies and keys can be synchronized with Active Directory to help speed deployments and reduce administration burdens.
- Key Recovery – Multiple recovery options allow organizations to determine the right solution for them to minimize potential lockouts and reduce HelpDesk calls.
- Single-Sign-On – SSO means fewer passwords for users to remember.
Key Benefits
- User-Friendly – Installation and registration is completely transparent to users, while CPU utilization during initial encryption is minimized to ensure that users can continue being productive while encryption happens in the background.
- Flexible – Support multi-user deployments in both Active Directory and non-Active Directory environments.
- Collaborative – Users can access encrypted data on removable media safely even on systems without Symantec Endpoint Encryption installed.
- Scalable – Scalable management architecture easily adapts to small and large enterprise environments.
- Stronger Protection – Symantec’s market leading Data Loss Prevention (DLP) software integrates with removable media encryption to analyze data before it’s transferred and automatically encrypt sensitive outgoing data.
Reference by : www.google.com