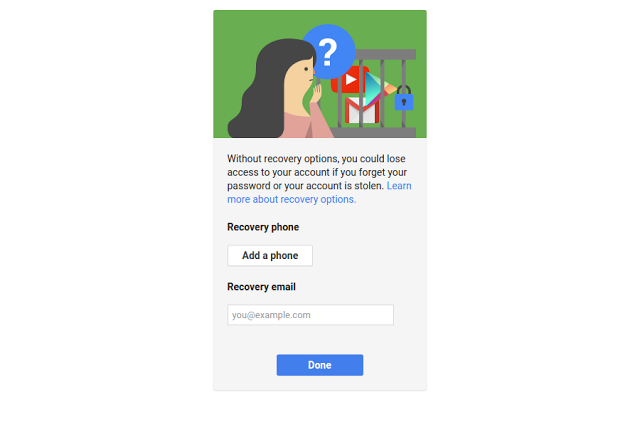
Helping users recover their password with recovery email addresses
If your domain has enabled non-admin user password recovery from the Admin console, then you may have decreased your help desk tickets by giving users an automated way to reset their password. Starting October 25, 2016, we’re extending non-admin user password recovery to include email addresses, an extension to our phone numbers launch from last year.
Non-admin user password recovery launched over a year ago as default OFF for new G Suite domains, and you can enable the feature by Organizational Unit from the Admin console under Security settings.
If you’ve already enabled the feature, then users will be prompted to add a secondary email address.
Security Best Practices
If you’ve enabled this feature for your domain, we’d like to remind you of the following resources for administrators we’ve updated with this launch:
Employee departure security best practices
Set password strength and user password recovery
Note: For G Suite for Education domains that are Primary/Secondary institutions, only administrators will be shown the prompt for email address and phone number.
Launch Details
Release track:
Launching to both Rapid release and Scheduled release on October 25, 2016
Rollout pace:
Gradual rollout (potentially longer than 3 days for feature visibility)
Impact:
All end users
Action:
Change management suggested/FYI
Reference by Google.com