Beware of Spora – a professionally designed ransomware
Spora is a recent addition to the ransomware family that Quick Heal Lab has come across. It is a file encryptor ransomware that encrypts a user’s files with strong encryption algorithm and demands a ransom. Spora is launched with a good infection routine, the capability to work offline, well-designed and managed payment portal dashboard, decryption key purchase options.
Infection Vector
Spora is delivered to the victim via spam emails containing a malicious .ZIP file as an attachment. This .ZIP file contains an HTML Application (‘.HTA’) file that pretends to be an invoice in .PDF or .DOC format, wearing double extensions to those files (e.g. <file_name>.pdf.HTA). As ‘Hide extensions for known file types’ option is marked checked by default in many systems, it increases the chances of getting trapped in opening an .HTA file by mistaking it for harmless file types.
Infection Routine
Spora has a multistage infection behavior. When a malicious .HTA file is executed, it drops and executes the below files into the system using VBScript program:
- ‘%Temp%\close.js’
- ‘%Temp%\doc_6d518e.docx’
• It is actually a file encryptor component that performs file encryption.
• doc_6d518e.docx is a corrupt file that is intentionally dropped and opened to keep the victim busy in viewing it while files are getting encrypted in the background.
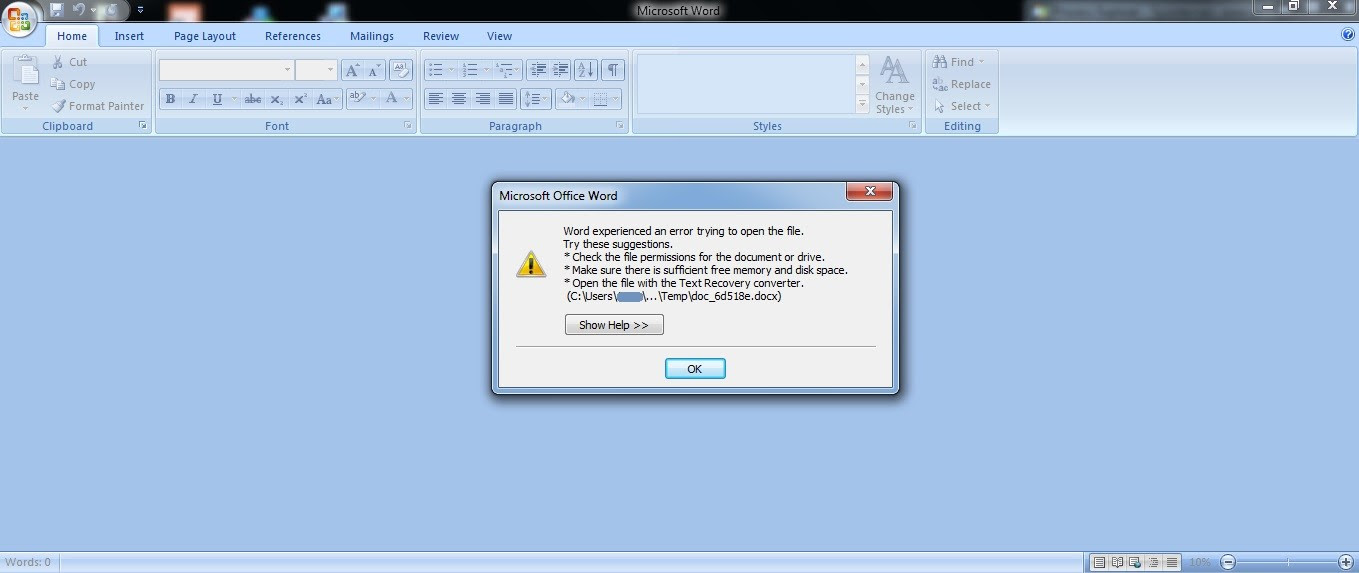
Figure 1: Corrupt document to fool a victim
Spora was not found appending any extension to the encrypted files. When encryption is over, a ransom note is displayed (shown below), highlighting the uniquely generated ‘Infection ID’ and basic instructions.
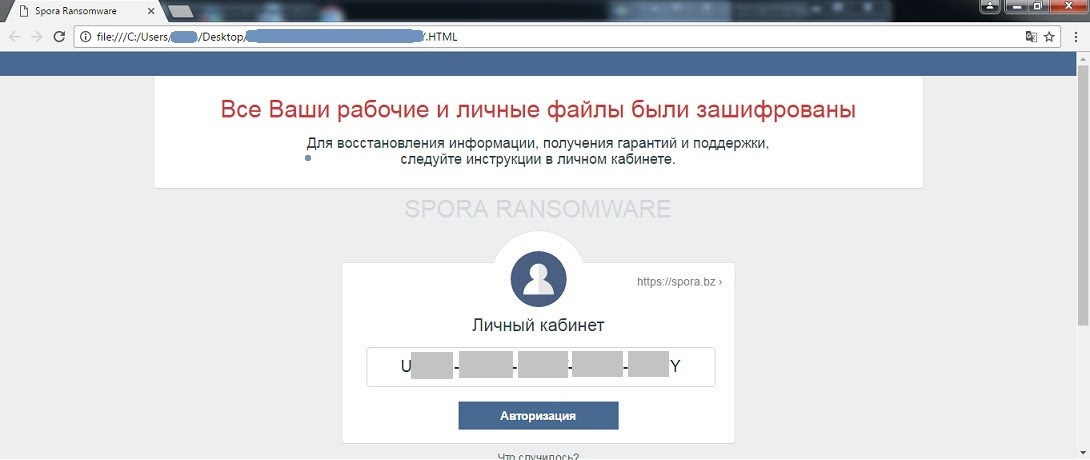
Figure 2. Spora ransom note with an infection ID
A .KEY file is dropped on the desktop, containing information about ‘encrypted-encryption keys’ used to encrypt files. In order for the victim to get complete access to the payment portal, they need to upload .KEY file to the portal to synchronize the infected computer with the payment portal. To do so, the below panel is provided.
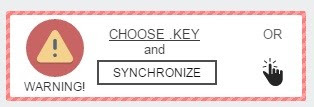
Figure 3. Key upload panel on Spora payment portal
Once synchronized, the victim can choose from a number of purchase options available on a ‘My Purchase’ section of the portal.
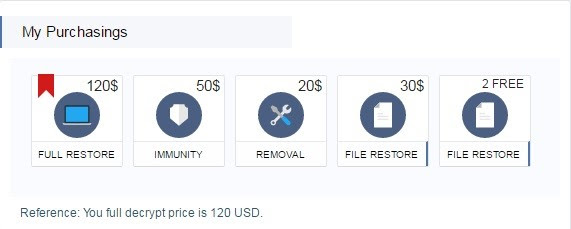
Figure 4. Decryptor purchase options
FULL RESTORE – With this, the user can have all their encrypted data restored.
IMMUNITY – With this, the user can buy immunity against future Spora attacks.
REMOVAL – With this, the user can have the Spora malware completely removed from their computer.
FILE RESTORE – Offers two options; decrypt two files for free or decrypt a selection of files for $30.
As you can see, Spora offers the victim with a variety of options to take care of the situation. For instance, a victim might be less likely to pay the ransom because they know they have safely backed up their data. However, they would still want to have the malware removed from the system – which gives the ‘Removal’ option.
Quick Heal Detection
Quick Heal antivirus successfully prevents Spora infections at multiple stages.
• Quick Heal Email Protection successfully prevents download of the malicious .ZIP attachment which is the first stage of the infection.
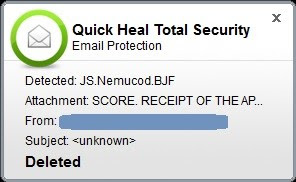
Figure 5. Quick Heal Email Protection
As shown in the image above, the malicious .HTA file has been successfully detected as ‘JS.Nemucod.BJF’ and deleted thereafter.
• Quick Heal Anti-ransomware protection successfully detects potential file encryption activities and alerts the user
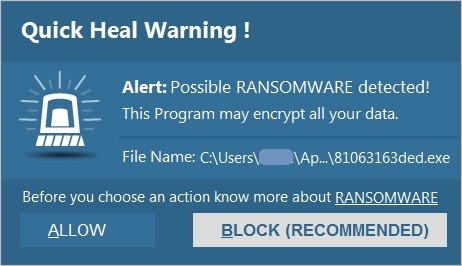
Figure 6. Quick Heal Anti-Ransomware alert
• Quick Heal Behavior Detection System successfully detects malicious activities and alerts the user
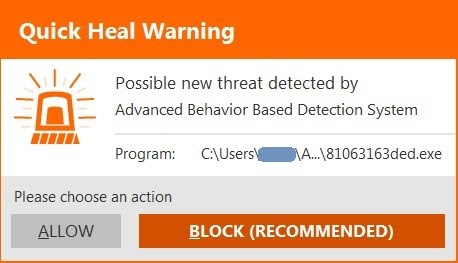
Figure 7. Quick Heal Behavior Detection System alert
Conclusion
It is not hard to guess that the creators of Spora have taken their time in developing this ransomware to make it effective, and professional at the same time.
A nicely designed decryptor portal dashboard, synchronization between the portal and infected system using a .KEY file, and multiple purchase option for decryption signify how attackers are using complex tactics in creating ransomware.
How to stay safe against such ransomware attacks
- Never download attachments that arrive in emails from unknown or unexpected sources.
- Take regular backups of your files. Remember to disconnect the Internet when you are backing up on a hard drive. Unplug the drive before you go online again.
- Apply all recommended security updates (patches) to your Operating System, and programs like Adobe, Java, web browsers, etc.
- Install an antivirus software that offers several layers of security. More importantly, keep the software up-to-date.
Reference by Quick Heal

